Current Vulnerable Hosts Breakdown
Current Vulnerable Hosts Breakdown report provides a breakdown of current vulnerable hosts and vulnerability instances ranked by count severity with asset-level detail. Use this report to gain insights into the effectiveness of your vulnerability management, help prioritize your efforts, and focus on specific areas in your environment.
To access the Current Vulnerable Hosts Breakdown report:
- In the Alert Logic console, click the menu icon (
 ), and then click
), and then click  Validate.
Validate. - Click Reports, and then click Vulnerabilities.
- Under Current Vulnerability Breakdown, click VIEW.
- Click Current Vulnerable Hosts Breakdown.
Filter the report
To refine your findings, filter your report by Customer Account, Deployment Name, VPC/Network, Asset Type, Category, Severity, and CVSS Score.
Filter the report using drop-down menus
By default, Alert Logic includes (All) values for most filters in the report.
To add or remove filter values:
- Click the drop-down menu in the filter, and then select or clear values.
- Click Apply.
Schedule the report
After you finish setting up the report, you can use CREATE REPORT to run it periodically and subscribe users or an integration (such as a webhook) to receive a notification when the report is generated. To learn how to schedule the report and subscribe notification recipients, see Scheduled Reports and Notifications.
Vulnerability categories
Alert Logic discovers several types of vulnerabilities, which are divided into categories, and referred to in sections of the report:
- Agent: Security vulnerability results detected by agent-based scans (on hosts with Agent-Based Scanning)
- Cloud Configuration: Security vulnerabilities detected by cloud/CIS compliance checks
- Credentials: Security vulnerabilities detected by credentialed internal network scans
- External: Security vulnerabilities detected by external network scans
- Network: Security vulnerabilities detected by unauthenticated internal network scans
CVSS severity categories
Alert Logic uses CVSS scores to measure the severity of vulnerabilities, which are divided into levels, and referenced to in some sections of this report.
Alert Logic assigns
| Severity rating | CVSS v2 score range | CVSS v3 score range |
|---|---|---|
|
|
Not applicable | 9.0 - 10.0 |
|
|
7.0 - 10.0 | 7.0 - 8.9 |
|
|
4.0 - 6.9 | 4.0 - 6.9 |
|
|
0.1 - 3.9 | 0.1 - 3.9 |
|
|
0.0 | 0.0 |
Some vulnerabilities in the National Vulnerability Database have both CVSS v2 and CVSS v3 scores. Alert Logic displays the newer CVSS v3 score and severity rating in prominent locations and both scores in detail views. If only one CVSS score exists, Alert Logic uses that score and severity rating.
Vulnerable Hosts section
This section provides the current total number of hosts with vulnerabilities in the selected filters.

Vulnerability Instances section
This section provides the current total number of vulnerability instances found in the selected filters.
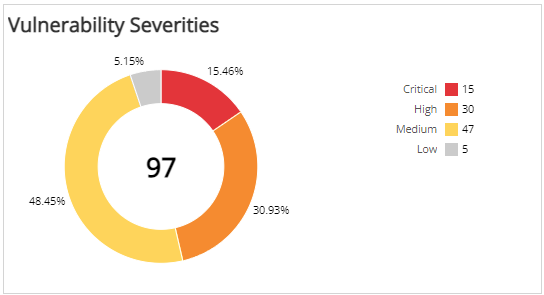
Vulnerability Severities section
This section provides the current vulnerability count in each CVSS severity category in the selected filters.
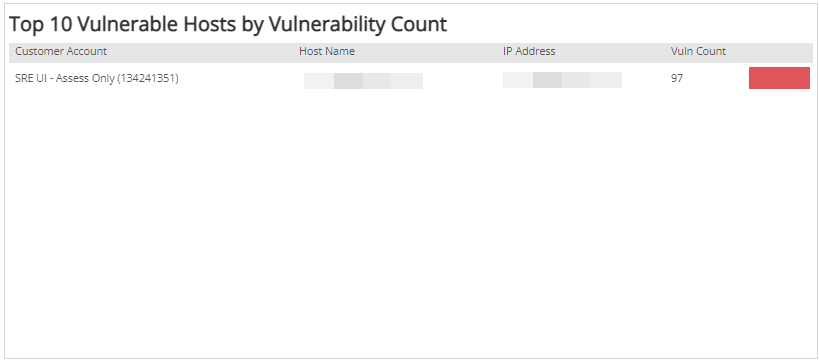
Top 10 Vulnerable Hosts by Vulnerability Count section
The list provides the current top 10 vulnerable hosts, based on the total vulnerability count in the selected filters. The list is organized by customer account, host name, IP address, count of vulnerabilities, and a bar graph representing the vulnerability count.
Top 10 Vulnerable Hosts by Severity section
The list displays the current top 10 vulnerable hosts based on the count of critical and high severity vulnerabilities in the selected filters. The list is organized by the customer account, host name, IP address, count of critical and high severity vulnerabilities, and a bar graph that represents the count of high severity vulnerabilities.

Vulnerable Hosts Breakdown Details section
The list provides the current breakdown of vulnerable hosts based on the vulnerability severity in the selected filters. The list is organized by IP address, host name, vulnerability, protocol/port, CVSS score, and the severity of the vulnerability.
